Of course they can. All they have to do is to make you install an .apk file on your Android smartphone or to download an application from Google Play store. Is that easy!
At a Black Hat conference held recently, a software security firm director, demonstrated in front of a live audience how easily one inexperienced hacker can breach your Android security firewalls and then proceed to install malicious software on your phone that can spy on your every move, breath and blink from dawn till dusk.
 |
| Android gone bad |
So, for example, let's take Instagram, an application downloaded by millions from Google Play store. A pimpled teenager, with moderate hacking skills, can in theory and in practice, take Instagram's harmless .apk, decompile it and place inside it a malevolent software and then repackage all off this back in to a normal Instagram .apk.
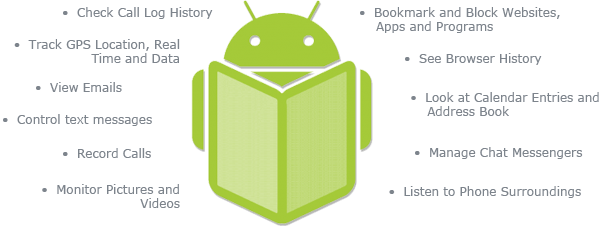
Once the user has installed this tempered Instagram .apk and the celestial alignment is right, one bad tempered teen from Iowa (or NSA, FBI and CIA all together) will be able to track all your smartphone's whereabouts. He can now easily read your sms and emails, remotely turn on your phone's camera and start taking incognito pictures and even record video clips, access all your call logs and, in general, he will be able to monitor everything you do on your phone. Or shall we say, his phone now. And all this without you noticing a thing!
 |
| A hacked Android. Your worst nightmare! |
Before we get all paranoid and start smashing our beloved Samsung Galaxy's and HTC One's, there are a few fact that we must take in consideration.
First of all, the ruthless hacker has to trick you in to installing his stained application. This can be done in two ways: he manages to get this malware infested Instagram on Google Play store, bypassing Google's security Cerberus ( a not that unimaginable endeavour in the not so distant past, but hardly possible nowadays) and the other method is to have you install applications .apk files from untrusted sources, outside the circle of trust and garden of Eden that has become Google Play store. The vast majority of users that have their phones malware infested did it by installing pirated applications from shady online harbours like Piratebay.
A plausible scenario is that right now we have legions of auto-spy android phone owners walking the streets, crowding the malls or coffee shops and unknowingly and innocently spying on everything that moves, not only them.
So, what can the average user do to reduce the risk of getting infested with this kind of malware? In order to avoid to transform your smartphone in to a 007 spyphone from hell, users must resist the temptation to download "free" (read pirated applications) from untrusted sources. The second best thing to do is to read the permissions that application asks. For example, if a game like Temple Run 2 will ask for permission to access your camera and phone logs, something isn't quite right, isn't it?
As for all our hackers wanna be, amateur code manipulators and software brewers out there... get out of the grey zone and put your talent to great use. Make a living. Find a job, put on a white hat and get paid for your insane skills!


No comments:
Post a Comment